Vulnerability assessments use automation to routinely scan for routers, firewalls, servers, applications, and switches. Web application penetration testing has a limited scope. A web application pen test uses numerous techniques to mimic an adversary’s planned actions or a user’s unintentional behaviors that may divulge sensitive information. These assessments expose weak spots in a web application’s inner workings.
As technology advances and our reliance on the Internet grows, cyber criminals now have several attack vectors to exploit. They go from website-to-website hunting for the next security weakness.
Web application penetration testing should be done before a production release. Due to time limitations, developers often deploy applications without proper security testing. As a result, certain web applications may have security issues.
Why do you need a Web App Pentest?
Businesses utilize web application penetration testing to enhance their overall security posture, improve site and application performance. While vulnerabilities are being investigated, data is gathered that can be used to pinpoint delays in application loading or response times. It can also assist in cross-browser compatibility testing.
These are just a handful of reasons for why you should conduct web application penetration testing:
- Identify Vulnerabilities
- Examine Security Policies
- Test Infrastructure
- Enhance Performance
- Meet Compliance Requirements
Identify Vulnerabilities
Web application penetration testing can help you find flaws in your application architecture. It can discover vulnerabilities that make sensitive data susceptible to attacks. It can also assist you in strengthening your security policies by exposing areas that require improvement.
Examine Security Policies
Organizations need relevant security measures. User authentication and password management are interdependent processes. Others deal with how security breaches are handled. Companies require policies for recognizing and reporting such threats. Amidst an attack, pondering what to do adds to the turmoil and raises the risk of future issues.
Test Infrastructure
Your public-facing infrastructure, such as firewalls, routers, and DNS servers, are dynamic. Constant changes are performed to better accommodate connections or to update traffic filter rules. Unintentional breaches are more likely when these adjustments are done in solitude. Testing your infrastructure is crucial to avoiding potential flaws.
Enhance Performance
A penetration test may be used to uncover issues with application load and response times by employing the proper testing methodologies. Testing application and infrastructure performance across a wide range of browsers and traffic levels gives the development team the information they need to make necessary modifications. Nothing is more aggravating than a delayed site load or a different home page in IE and Chrome.
Comply with Regulations
Depending on your sector, penetration testing may be necessary for compliance. For example, PCI DSS regulations mandates regular penetration tests if you are storing sensitive personal or financial information/. A web application penetration test can help your company accomplish more than simply comply with regulations.
Our penetration tests will assist you in the following ways:
- Identify vulnerabilities.
- Investigate any security findings that may allow data theft.
- Find the most susceptible attack vectors.
- Improve your overall security posture.
- Establish robust authentication and authorization controls.
- Develop strong access controls.
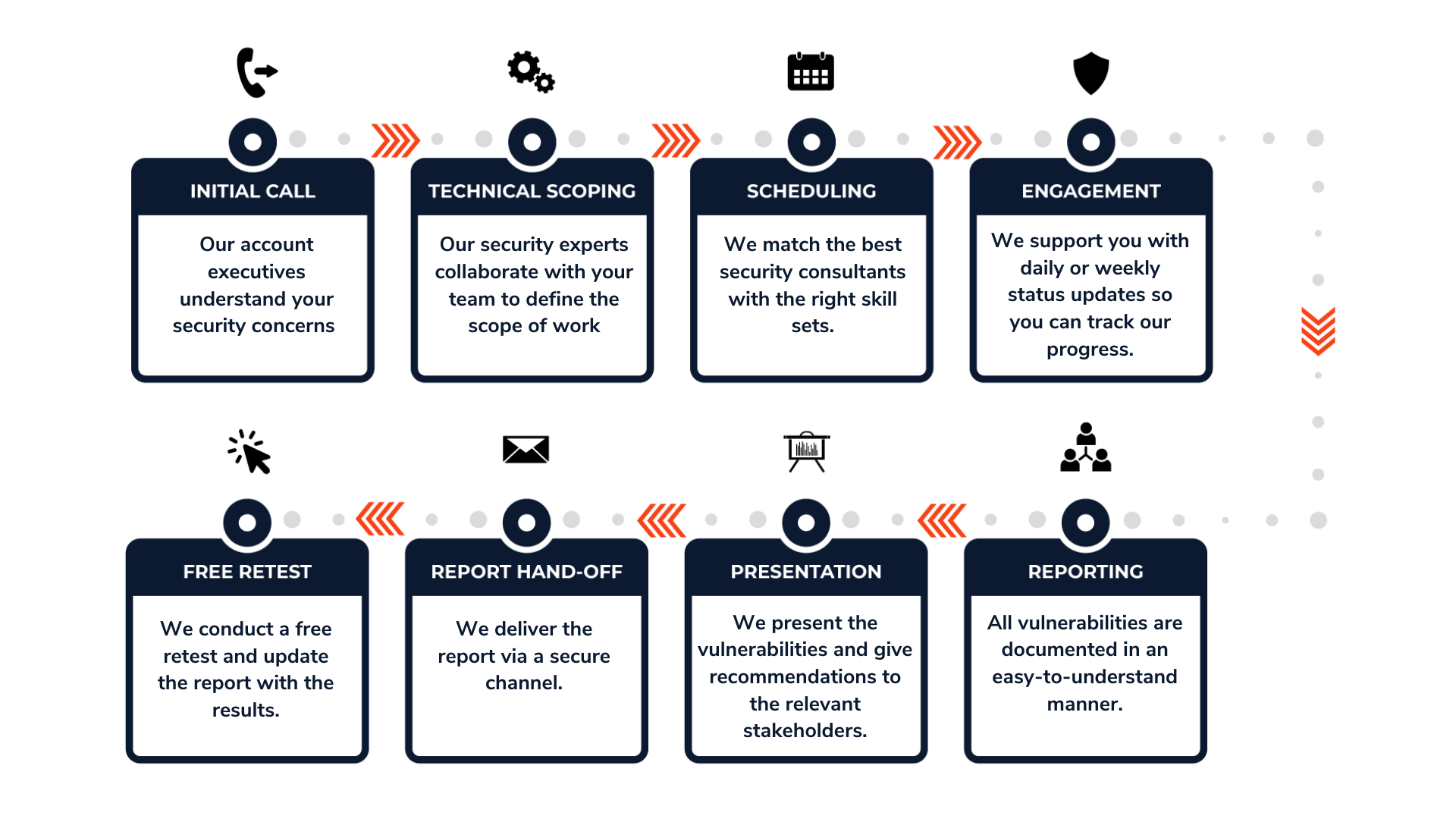
Our Approach
Our certified penetration testers use a proven approach that relies on the OWASP Top 10 Application Security Risks. This method uses many of the same tools as an attacker. For more details, reach out to us at info@redfoxsec.com.
What to Expect?
By partnering with Redfox Security, you’ll get the best security and technical skills required to execute an effective and thorough penetration test. Our offensive security experts have years of experience assisting organizations in protecting their digital assets through penetration testing services. To schedule a call with one of our technical specialists, call 1-800-917-0850 now.
Redfox Security is a diverse network of expert security consultants with a global mindset and a collaborative culture. If you are looking to improve your organization’s security posture, contact us today to discuss your security testing needs. Our team of security professionals can help you identify vulnerabilities and weaknesses in your systems and provide recommendations to remediate them.
“Join us on our journey of growth and development by signing up for our comprehensive courses.“